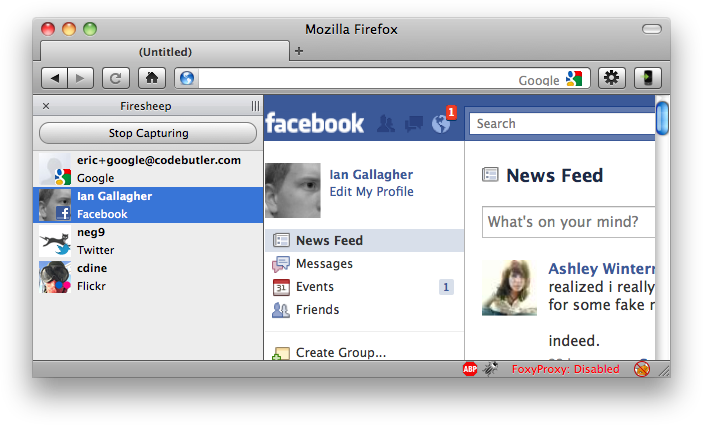
On Sunday, Eric Butler released Firesheep, and in doing so has unleashed a new security risk that applies to anyone logging into websites on public Wi-Fi. It is now disturbingly easy to masquerade as a facebook or twitter user, for instance.
After you log in on a website, that site transmits a cookie to your computer. This is how you stay logged in as you travel from page to page during your session. The Firesheep extension allows anyone using it to sniff out and capture these cookies as they are transmitted from the wireless router you are connected to.
There is a way to Protect from Firesheep using Firefox, although it’s not guaranteed to work across all sites. Your best protection is to abstain from logging into no SSL encrypted sites when you’re on a public wireless network. Some websites, such as your Bank or PayPal always use SSL (look for the ‘https://’ and not ‘http://’) are immune because all communication between your web browser and the server is encrypted.